General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsSnowden Mentioned Direct Access In Interview With The Guardian
Edward Snowden, the former National Security Agency contractor who leaked top secret agency documents to the media, said during an on-camera interview with The Guardian last month that the NSA's PRISM program gives the government "direct access" to major technology companies' systems.
"We've got PRISM, which is a demonstration of how the U.S. government co-opts U.S. corporate power to its own ends," Snowden said during a new portion of the interview, conducted on June 6, which The Guardian released on Monday. "Companies like Google, Facebook, Apple, Microsoft -- they all get together with the NSA, and provide the NSA direct access to the back ends of all of the systems you use to communicate, to store data, to put things in the cloud, and even just to send birthday wishes, and keep a record of your life. And they give [the] NSA direct access that they don't need to oversee, so they can't be held liable for it."
Soon after NSA documents related to PRISM and descriptions of the program appeared in The Guardian and The Washington Post, Apple, Facebook, and Google explicitly denied giving the government "direct access" to company servers. In a blog post in June, The Guardian's Glenn Greenwald said that the newspaper's original article about PRISM "did not claim that the NSA document alleging direct collection from the servers was true; we reported - accurately - that the NSA document claims that the program allows direct collection from the companies' servers."
Snowden did not mention "direct access" in the original portion of the video interview released last month, but when asked about what the phrase meant during a live chat on The Guardian's website last month, he wrote that "
http://livewire.talkingpointsmemo.com/entry/snowden-mentioned-direct-access-in-interview-with-guardian
Here's what the Snowden videos did
http://www.democraticunderground.com/10023203719
Waiting For Everyman
(9,385 posts)Trashing.
ProSense
(116,464 posts)BehindTheCurtain76
(112 posts)There is no government by the people anymore and we have wasted the last 5 years by smugly thinking anything has changed. Things are way worse now and will keep getting that way regardless if it's a republican or democrat in office because whoever is elected is expected to play ball or get Wellstoned.
reusrename
(1,716 posts)They absolutely do have direct access. They just don't contract with the providers for it. There are contractors that provide the direct access.
http://www.subsentio.com/service-providers/electronic-surveillance-standards/
That way the telecoms still enjoy their not-so-plausible deniability.
In the industry it's referred to as "safe harbor" or "lawful compliance."
ProSense
(116,464 posts)Cha
(297,289 posts)OnyxCollie
(9,958 posts)From March, 2008.
For civil liberties advocates, the first week of March 2008 wasn’t shaping up very well. For months, the House of Representatives had
been wrangling to work out a compromise bill for a pressing issue – anti-terrorist spying legislation. That political hot-button
guaranteed a tremendous amount of media coverage, as the bill represents Congress’ response to the “domestic spying” scandal
plastered on the front pages of newspapers for years – proof that the Bush administration had violated the privacy rights of American
citizens by circumventing the Foreign Intelligence Surveillance Act (FISA) requirements to secure judicial warrants to target monitor
citizen’s communications.
~snip~
That’s when GAP helped our client, Babak Pasdar, educate our representatives on the full scope of what information certain telecoms
provided to the Bush administration. In a word – everything. Pasdar’s disclosures shocked Congress, and delayed the vote.
The “Quantico Circuit”
Pasdar, a experienced computer expert, was hired as a contractor to do security work for a major telecommunications company. In
doing so, he discovered a mysterious “Quantico Circuit” at the company’s facility (media sources identified the telecom as Verizon).
The circuit, linked to Quantico, VA, provided the federal government unfettered access to all of that company’s customer mobile phone
communications – all calls, emails, text messages, internet use, videos, billings, and even customer locations. However, the line was
configured so no record of what was being tapped by the government existed.
Pasdar stated that logs should be kept of what was recorded, but he was quickly moved off the project. When the telecommunications
immunity vote seemed imminent, he knew he had to expose his finding to the country before judgment was passed. How could any
immunity be reasonable, or just, if the full violations were not known? Pasdar sought help from GAP.
My name is Babak Pasdar, President and CEO of Bat Blue Corporation. I have given this affidavit to
Thomas Devine, who has identified himself as the legal director of the Government Accountability
Project, without any threats, inducements or coercion.
I have been a technologist in the computer and computer security industry for the past nineteen years
and am a "Certified Ethical Hacker" (E-Commerce Consultants International Council.) I have worked
with many enterprise organizations, telecommunications carriers, as well as small and medium sized
organizations in consulting, designing, implementing, troubleshooting, and managing security systems.
This statement is to make a record ofmy concerns about the privacy implications for our society from
what I personally witnessed at a major telecommunications carrier, as summarized below.
~snip~
Our plan that evening was to migrate a set of users to the new firewall, and then determine if and how it
impacted access and functionality. We started testing and, all-in-all, the small users test migration went
very well. The test went so well that we then set out to migrate over 300 sites that were carrier owned
or affiliate locations. These 300 or so sites were mostly sales offices. We migrated the locations by
redirecting their traffic to the new firewalls. All was going extremely well. As the night went on you
could feel the relief taking over the anxiousness everyone had felt earlier.
At one point I overheard C1 and C2 talking about skipping a location. Not wanting to do a shoddy job
I stopped and said "we should migrate all sites."
C1 told me this site is different.
I asked, "Who is it? Carrier owned or affiliate?"
C1 said, "This is the 'Quantico Circuit.'''
I remember that he paused and looked at me as did C2. I inquired, "Quantico, Virginia? Is this a store
location?"
C1 responded, "No."
"Is it what I think it is?", I asked.
C1 did not reply but just smiled. It was a very telling smile and I knew we were discussing something
unusual.
"What kind of circuit is it?", I asked.
"A DS-3," replied C1. (A DS-3 is a 45 mega bit per second circuit that supports data and voice
communications.)
C1 said that this circuit should not have any access control. He actually said it should not be
firewalled.
I suggested to migrate it and implement an "Any-Any" rule. ("Any-Any" is a nickname for a
completely open policy that does not enforce any restrictions.) That meant we could log any activity
making a record ofthe source, destination and type of communication. It would have also allowed
easy implementation of access controls at a future date. "Everything at the least SHOULD be logged," I
emphasized.
C1 said, "I don't think that is what they want."
"Who?", I asked, and again C1 and C2 did not respond.
C2 by this point had stepped back and his body language showed that he was very uncomfortable
discussing this matter.
"Come on guys, let's just do it and ask for forgiveness later. You know its the right thing." I suggested.
C1 and C2 did not want to comply. Instead they got on the phone with DS who asked me to stop what I
was doing and move on. To my surprise, he then drove the one hour or so to the data center.
The tentative, uncertain DS I had known was transformed into a man wagging his finger in my face and
telling me to "forget about the circuit" and "move on" with the migration, and ifI couldn't do that then
he would get someone who would.
I politely and in a low-key manner informed DS that my intention was to deliver security in line with
industry-acceptable use scenarios, and although I am not intimately familiar with their security policy,
it was reasonable to think that having a third party with completely open access to their network core
was against organizational policy.
DS did not want to hear any of it and re-doubled his emphatic message to move on. This was serious
stuff. He had let me know in no uncertain terms that I was treading above my pay grade.
When DS left, I asked C1 again, "Is this what I think it is?"
"What do you think?", he replied again, smiling.
I shifted the focus. "Forgetting about who it is, don't you think it is unusual for some third party to have
completely open access to your systems like this? You guys are even firewalling your internal offices,
and they are part of your own company!"
C1 said, "Dude, that's what they want."
I didn't bother asking who "they" were this time. "They" now had a surrogate face - DS. That told me
that "they" went all the way to the top, which was why the once uncertain DS could now be so sure and
emphatic.
Hydra
(14,459 posts)I've seen the stuff about AT&T but this adds to evidence.
I think this is what the Admin REALLY doesn't want us to see- full access built into the system.
grasswire
(50,130 posts)It is just extraordinary. I encourage you to make a separate OP of it so that everyone can see it. Thank you for posting it.
Cali_Democrat
(30,439 posts)But remember, it's not about Snowden, it's about his claims.
Oh wait...WTF?
![]()
BehindTheCurtain76
(112 posts)Keep spreading the misinformation. Why keep pushing these lies? We need more interviews with whistleblower Russ Tice not baseless accusations. Assuming your comment wasn't sarcasm.
VanillaRhapsody
(21,115 posts)He certainly hasn't made their lives easier....I bet he doesn't have many friends among them anymore.You know ones that actually obey the laws. (Just because you CAN drive over 100 mph....doesn't mean that you have done it....very damn few people have done that). If what he is contending were true....wouldn't there be more willing to stand with him...you know the old "I am Edward Snowden" type scenario?
That's the reason you haven't heard any of them come forward to support his contentions...is that he has probably made their lives incredibly difficult as well.
reusrename
(1,716 posts)What's different about their jobs now?
VanillaRhapsody
(21,115 posts)What's different? Do you realize how much new bullshit has just been rained down on them?
reusrename
(1,716 posts)As for the robosigning, it's all there in the information that has been released. The analysts simply fill out a form or template and they have immediate access to the contents of emails and phone calls.
The template or form drives all of the computer modules that compile all the information needed for requesting a warrant from the FISA court. This ensures that the requirements for the warrant are complied with.
Then, sometime during the following 72 hours, the warrant request is sent to the FISA court. It is automatically approved since all the "legal" requirements have been met when the analyst completes the form or template that starts the process. I imagine thousands of communications can be requested by a single warrant.
Any analyst is authorized to obtain the content of any voice or email record, on his own authority, if he has been verbally authorized to do so by either the Attorney General or the Director of National Intelligence.
It's all covered in the FISA law itself, and then made crystal clear by the document releases that Snowden made. The laws were already known, Snowden explains the policy used to implement the law, which I never heard anything about before his disclosures.
If you are familiar with how robosigners were used to flout legal hurdles in the home repossession scandals, then you have to understand that this system of having the analysts become robosigners is done for exactly the same purpose. The only difference being that in the NSA spying case the robosigning has been made the official policy, which I think makes it legal, even though it violates the spirit of the law.
The policy could be ruled illegal by the Supreme Court, but no one has been able to argue the case there because all Americans lack legal standing.
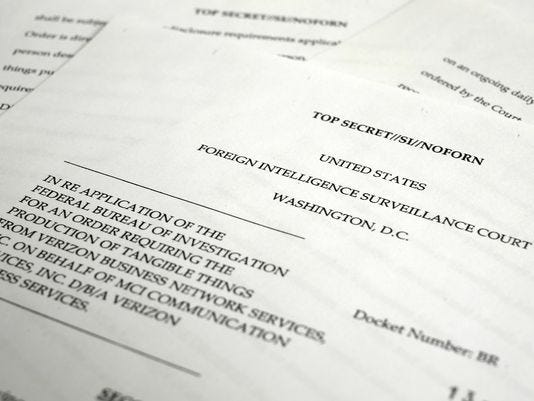
One of the documents that Snowden released was the Verizon warrant which should provide legal standing to Verizon customers since they can now prove to the court that they are being targeted. In the past the court denied standing to everyone because no one could really know whether or not they were on a list since it was all secret.
 ?87cc7ae5b5e3d133be9f113f907a13faa9f8741e
?87cc7ae5b5e3d133be9f113f907a13faa9f8741e
So what's been raining down on them?
.
BehindTheCurtain76
(112 posts)Snowden is the real Amerucan hero. He protects the freedoms of our people as others destroy them with apologists giving them cover. No one killing families in TE middle east are protecting our freedoms. The war on terror is a scam.
reusrename
(1,716 posts)People are being manipulated into thinking a certain way.
It is very deliberate and very scientific. It's the best weapon for controlling a society that has ever been developed. As long as it remains in the dark no one can really be blamed for being a victim of it. At this stage shining light on it may not change things much.
I don't do blame the victim stuff very well.
BehindTheCurtain76
(112 posts)Jusy like the sock puppet profile software where one intelligence analyst can control 100 fake online profiles to comment or blog from and try to sway public opinion online. It's all about consensus reality.
reusrename
(1,716 posts)Basically, the law requires someone to certify certain things. In the case of the mortgage thefts they robosigned all sorts of documents saying that they had reviewed the original paperwork on the transaction and stuff like that. They never even had the paperwork in most cases, but they hired people to swear that they did, and that they had reviewed it all.
In the spy analyst case it's sort of the same thing, only now it's official policy. An actual person has to certify (for instance) that if we don't listen to this specific call or read this specific email then we will all die at the hands of terrorists.
So what they've done is they have set up a system where (most likely, because I don't really know too many details of this software) when an analyst logs onto the system his authorization code (or electronic signature) is automatically attached to every transaction that he does. Hence the robosigning analogy.
In order to have this authority to robosign this stuff, he only has to be verbally authorized to do so by either the Attorney General or the Director of National Intelligence.
Apparently he has instant access, on his own authority, to the pretty much the entire database.
I hope that helps a little.
BehindTheCurtain76
(112 posts)We need checks and balances...not trust. The banks lie on a massive scale just like the government and police agencies do. If they could get away with it we would all be on concentration slave camps. Anyone who excuses them is as bad as they are.
reusrename
(1,716 posts)It may be much simpler to fix most of this than we think. There are some smart people out there.
I was thinking about the recent airliner crash being the only fatal commercial accident in over 2 years. Think about the tension that exists in that industry between safety and profits. And yet is can be safe and profitable. It isn't a zero sum gain at all. Safer aircraft cost more, but they also earn more, or something along those lines.
The way the costs are kept low while safety is assured is that everyone job in the industry has to be certified. And mechanics, pilots, crew members all exist in a framework that is based on an honor system. And it works.
We need to implement a similar system to regulate Wall Street. We need to move this from a fraud-based economy to a trust-based economy. That can be easily accomplished by making people accountable and providing them the proper training to monitor the finance sector as rigidly as we monitor the aviation sector.
VanillaRhapsody
(21,115 posts)this is your contention?
reusrename
(1,716 posts)Explain it to me.
VanillaRhapsody
(21,115 posts)If someone on YOUR job pulled an illegal and highly criminal act....would there be fallout? These are guys who are already under far far more scrutiny than YOUR job....so you figure it out!
Robosigners...THAT'S the kind of thing High Level Top Secret Analysts for the NSA want to be called I am sure!
reusrename
(1,716 posts)Why don't you just tell me what you mean?
And the robosigner comparison is MY analogy, not something that you can fairly blame Snowden for.
VanillaRhapsody
(21,115 posts)reusrename
(1,716 posts)VanillaRhapsody
(21,115 posts)and if true doesn't that make him and even bigger liar??
reusrename
(1,716 posts)My main interest is in researching how our social networks are being mapped by the NSA
and how this information is used to thwart our ability to organize any political resistance.
Snowden had more than one job using this system.
His last job was working as an analyst.
Before that he had other jobs as a systems software person.
I am quite confident that Snowden understands the architecture of the software.
I can understand being skeptical, but hasn't he been right about everything?
dkf
(37,305 posts)ProSense
(116,464 posts)dkf
(37,305 posts)New info.
ProSense
(116,464 posts)grasswire
(50,130 posts)That's some ugly stuff.
Cali_Democrat
(30,439 posts)Oh please!